Enable Login on the Vty Lines Using the Local Database Updated FREE
Enable Login on the Vty Lines Using the Local Database
7.2.6 Parcel Tracer – Configure Local AAA for Console and VTY Access Answers Version
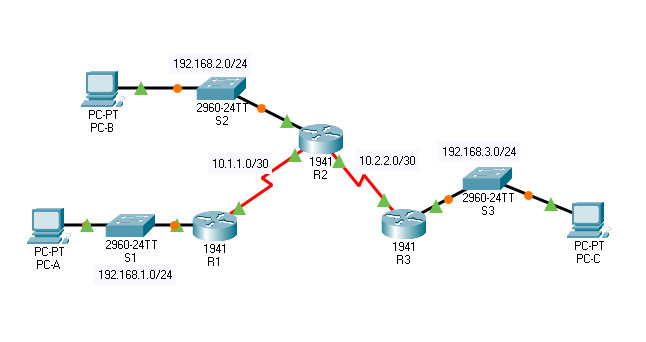
Topology
vii.2.six Packet Tracer – Configure Local AAA for Console and VTY Access
Addressing Tabular array
| Device | Interface | IP Address | Subnet Mask | Default Gateway | Switch Port |
|---|---|---|---|---|---|
| R1 | G0/1 | 192.168.ane.1 | 255.255.255.0 | Northward/A | S1 F0/1 |
| S0/0/0 (DCE) | 10.1.1.ii | 255.255.255.252 | N/A | N/A | |
| R2 | G0/0 | 192.168.2.1 | 255.255.255.0 | N/A | S2 F0/two |
| S0/0/0 | 10.1.1.1 | 255.255.255.252 | N/A | N/A | |
| S0/0/1 (DCE) | x.2.2.1 | 255.255.255.252 | N/A | N/A | |
| R3 | G0/one | 192.168.3.i | 255.255.255.0 | N/A | S3 F0/five |
| S0/0/1 | x.two.2.ii | 255.255.255.252 | N/A | Due north/A | |
| PC-A | NIC | 192.168.i.three | 255.255.255.0 | 192.168.one.i | S1 F0/ii |
| PC-B | NIC | 192.168.2.three | 255.255.255.0 | 192.168.ii.1 | S2 F0/1 |
| PC-C | NIC | 192.168.iii.three | 255.255.255.0 | 192.168.three.ane | S3 F0/18 |
Objectives
- Configure a local user account on R1 and configure authenticate on the console and vty lines using local AAA.
- Verify local AAA hallmark from the R1 console and the PC-A client.
Background / Scenario
The network topology shows routers R1, R2 and R3. Currently, all administrative security is based on knowledge of the enable secret countersign. Your task is to configure and test local and server-based AAA solutions.
You will create a local user account and configure local AAA on router R1 to test the console and vty logins.
- User account: Admin1 and password admin1pa55
The routers have too been pre-configured with the post-obit:
- Enable hush-hush countersign: ciscoenpa55
- OSPF routing protocol with MD5 hallmark using password: MD5pa55
Note: The console and vty lines have not been pre-configured.
Note: Newer IOS images apply more secure encryption hashing algorithm; yet, the IOS version currently supported in Packet Tracer uses MD5. E'er employ the near secure pick available on your physical equipment.
Office 1: Configure Local AAA Authentication for Panel Access on R1
Step 1: Configure a local username on R1.
Configure a username of Admin1 with a secret password of admin1pa55.
R1(config)# username Admin1 underground admin1pa55
Step 2: Configure local AAA authentication for console access on R1.
Enable AAA on R1 and configure AAA authentication for the console login to use the local database.
R1(config)# aaa new-model R1(config)# aaa authentication login default local
Pace three: Configure the line console to utilise the defined AAA authentication method.
Enable AAA on R1 and configure AAA authentication for the console login to apply the default method list.
R1(config)# line console 0 R1(config-line)# login authentication default
Step 4: Verify the AAA authentication method.
Verify the user EXEC login using the local database.
R1(config-line)# end %SYS-5-CONFIG_I: Configured from console by console R1# exit R1 con0 is at present available Printing Render to get started. ************ AUTHORIZED Admission ONLY ************* UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED. User Access Verification Username: Admin1 Password: admin1pa55 R1>
Function ii: Configure Local AAA Authentication for vty Lines on R1
Stride 1: Configure domain name and crypto key for utilise with SSH.
a. Use netsec.com as the domain name on R1.
R1(config)# ip domain-name netsec.com
b. Create an RSA crypto cardinal using 1024 bits.
R1(config)# crypto cardinal generate rsa general-keys modulus 1024 The name for the keys will exist: R1.netsec.com % The key modulus size is 1024 bits % Generating 1024 fleck RSA keys, keys volition be not-exportable…[OK] *Mar ane 0:2:12.822: %SSH-v-ENABLED: SSH 1.99 has been enabled
Step ii: Configure a named list AAA hallmark method for the vty lines on R1.
Configure a named list called SSH-LOGIN to cosign logins using local AAA.
R1(config)# aaa authentication login SSH-LOGIN local
Step 3: Configure the vty lines to use the defined AAA authentication method.
Configure the vty lines to use the named AAA method and only allow SSH for remote access.
R1(config)# line vty 0 4 R1(config-line)# login authentication SSH-LOGIN R1(config-line)# transport input ssh R1(config-line)# end
Step 4: Verify the AAA authentication method.
Verify the SSH configuration SSH to R1 from the command prompt of PC-A.
PC> ssh –l Admin1 192.168.i.1 Open Password: admin1pa55
Answer Script
Router R1
enable config terminal username Admin1 hole-and-corner admin1pa55 aaa new-model aaa authentication login default local line panel 0 login hallmark default ip domain-proper name netsec.com crypto key generate rsa general-keys modulus 1024 aaa authentication login SSH-LOGIN local line vty 0 4 login authentication SSH-LOGIN send input ssh
Download seven.2.6 Packet Tracer – Configure Local AAA for Console and VTY Admission PDF & PKA files:
[sociallocker id="54558″]
[/sociallocker]
Enable Login on the Vty Lines Using the Local Database
DOWNLOAD HERE
Source: https://itexamanswers.net/7-2-6-packet-tracer-configure-local-aaa-for-console-and-vty-access-answers.html
Posted by: nelsontyrdeed.blogspot.com